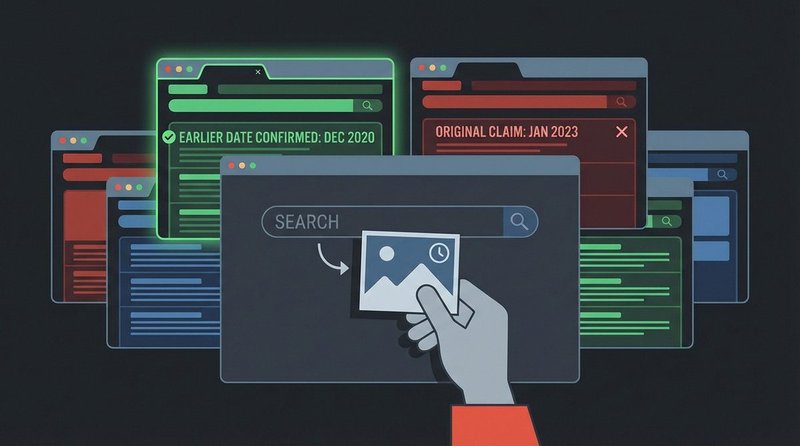
Reverse image search lets you trace any photograph back to its original context — finding when it was first published, where it came from, and whether it has been used to misrepresent a different event. It takes 30 seconds and catches one of the most common patterns in visual misinformation: recycled photographs presented as current documentation.
Why Visual Misinformation Requires Specific Tools
Images carry an implicit credibility that text does not. A photograph feels like evidence. That intuition is exploited systematically in misinformation: real photographs from different places, different years, or different events are attached to new captions that misrepresent what they show. The image is authentic; the context is fabricated.
Bellingcat, BBC Verify, and Storyful documented this pattern extensively during the 2022 Russian invasion of Ukraine. Within the first month of the invasion, Storyful’s verification team flagged at least 23 distinct recycled-image incidents, including a widely shared photograph of a tank column traced to a 2016 Syrian Arab Army operation. See the Recycled War Photos case in the database → for the documented record.
Reverse image search does not detect AI-generated imagery directly — for that, see the Deepfakes Identification Guide →. What it does reliably: locate earlier appearances of a photograph that prove it predates the event it claims to document.
The Three Tools You Need
Use at least two search engines per verification task. Different platforms crawl different portions of the web and index images at different times — what Google misses, Yandex or TinEye may surface.
Google Images
Google Lens is the most comprehensive reverse image search by index size. On desktop, navigate to images.google.com and click the camera icon to upload an image file or paste a URL. On mobile Chrome, long-press any image to trigger “Search image with Google.” After results appear, use the Tools > Time filter to find the earliest indexed appearance of the image — this is often the most useful single step for detecting recycled visuals.
Google Lens also identifies objects, text, and locations within images, which is useful for geolocation (confirming whether a landmark, road sign, or vegetation type is consistent with the claimed location).
TinEye
TinEye specializes in finding exact and near-exact copies of images regardless of filename, metadata, or minor edits. Unlike Google, TinEye uses perceptual image fingerprinting — it can match a cropped or color-adjusted version of a photograph back to the original. Search results include the first indexed date for each match, which TinEye displays as its primary sort option. For recycled images, sort by “Oldest” to immediately surface the earliest known appearance.
TinEye does not rely on EXIF data or image metadata, which means it works even when metadata has been stripped.
Yandex Images
Yandex Images is particularly effective for photographs originating from Russian-language, Eastern European, and Central Asian sources. Its facial recognition capabilities are stronger than Google’s for identifying individuals in photographs. For conflict documentation, Yandex often surfaces results that Google does not index, particularly from Telegram channels and Russian social media platforms. Navigate to Yandex Images and click the camera icon to upload or paste a URL.
Step-by-Step: Verifying a Photograph
Follow these steps in order. You can stop at any point if you have enough information to make a verification decision.
- Run Google Images first. Upload the image or paste its URL. Review the top results for any appearance that predates the claim you are evaluating. Use Tools > Time to narrow the date range.
- Run TinEye second. Sort results by “Oldest” to see the earliest indexed appearance. If TinEye returns a result dated before the event the image claims to document, the image has been recycled.
- Run Yandex if the first two are inconclusive. Yandex is particularly useful for images connected to Eastern European or Russian-language sources.
- Check the EXIF metadata if you have access to the original file. Use Exif.tools or the free browser extension Forensically. EXIF data includes capture date, camera model, and GPS coordinates where available. Note: EXIF data can be stripped or altered, so absence of metadata is not conclusive either way.
- Cross-reference with the claimed location. If the image shows an outdoor environment, use Google Street View, Google Earth, or GeoGuessr-trained geolocation to verify whether the visible architecture, vegetation, road markings, or signage are consistent with the claimed country or city.
- Record your findings. Note the earliest confirmed date of appearance, the source, and any discrepancy between the claimed and verified context. This documentation matters if you are correcting a public post or filing a report.
Dealing With Cropped, Filtered, and Edited Images
Visual misinformation frequently modifies images before recycling them: cropping removes identifying context at the edges, color filters change mood, and brightness adjustments obscure details. A modified image can defeat standard reverse image search if the modification is significant.
If standard reverse image search fails on a visually suspicious image, try these approaches:
- Crop to a distinctive section. If the background or environment is more distinctive than the foreground subject, crop to that portion and search separately. Architectural features, landmarks, and vegetation patterns often survive cropping intact.
- Remove the image from its immediate context. Screenshots of images from social media posts often include interface elements (like-counts, platform logos) that confuse reverse image engines. Screenshot just the photograph itself and search that crop.
- Try Bing Visual Search. Microsoft’s Bing Visual Search uses a different index and object-recognition algorithm — it occasionally surfaces results that Google and TinEye both miss, particularly for images from North American and European sources.
- Use InVID/WeVerify for video frames. The InVID WeVerify browser plugin (free, Chrome and Firefox) extracts keyframes from any video URL and runs reverse image searches on each frame simultaneously. This is the standard tool used by professional fact-checkers for video verification.
Reading EXIF Metadata: What It Tells You and What It Does Not
EXIF (Exchangeable Image File Format) data is metadata embedded in JPEG, TIFF, and some PNG files at the moment of capture. It can include: capture date and time, GPS coordinates of where the photo was taken, camera manufacturer and model, lens focal length and aperture settings, and software used to process the file.
What EXIF tells you when present: a GPS coordinate that places the image in a different country than claimed is strong evidence of out-of-context use. A capture date that predates the event the image claims to document is definitive. A software field showing professional editing software (Photoshop, Lightroom) does not mean manipulation — most photojournalists edit for exposure and color — but unusual processing entries can be informative.
What EXIF does not tell you: EXIF data is removed automatically by most major social media platforms on upload — Facebook, Instagram, and Twitter/X strip metadata to reduce file size. An image circulating on social media will almost always lack EXIF data. This absence is not suspicious; it is normal. Absence of EXIF proves nothing about an image’s authenticity or origin.
Additionally, EXIF data can be manually edited using freely available tools. A fabricated capture date in EXIF is technically possible. Treat EXIF data as corroborating evidence, not as definitive proof.
Practical Limits of Reverse Image Search
Reverse image search is one of the most reliable first steps in visual verification, but it has documented limits. AI-generated images — faces, scenes, and objects that do not exist in any prior photograph — will return no matches because there is no original to find. For those cases, different detection methods apply (see the Deepfakes Guide). Very new photographs published for the first time during a breaking news event may not yet be indexed; run searches again 12–24 hours later. And some legitimate photographs simply do not appear in major search indexes — particularly images from less-indexed regions or private archives.
A negative result (no matches found) is not confirmation that an image is authentic. It means it has not been previously indexed in the databases you searched. Combine reverse image search with EXIF analysis and geolocation for a more complete picture, and apply the SIFT method → to the source publishing the image regardless of what visual search returns.
Quick-Reference: Reverse Image Search Checklist
- Run Google Images — use Tools > Time to find the earliest appearance.
- Run TinEye — sort by “Oldest” to surface the earliest indexed version.
- Run Yandex for images connected to Eastern European or Russian-language sources.
- Check EXIF metadata using Exif.tools or Forensically if the original file is accessible.
- Geolocate outdoor images using Street View or Google Earth to verify claimed location.
- For video: use InVID/WeVerify to extract keyframes and run reverse searches on each.
- A negative result is not confirmation of authenticity — it means the image is not indexed.